Breakdown of /var/log/auth.log, what is ssh2?
By John Parsons •
I've used the command grep sshd.\*Failed /var/log/auth.log | less to check how much brute force traffic is on my Ubuntu 18.04 LTS machine. I've noticed a few parts I don't understand.
Nov 21 12:55:53 *LOCALHOSTNAME* sshd[31151]: Failed password for invalid user john from *EXTERNAL IP* port 52162 ssh2
Nov 21 13:28:22 *LOCALHOSTNAME* sshd[31180]: Failed password for root from *EXTERNAL IP* port 47906 ssh2
Nov 21 13:37:03 *LOCALHOSTNAME* sshd[31186]: Failed password for root from *EXTERNAL IP* port 56522 ssh2
Nov 21 13:44:06 *LOCALHOSTNAME* sshd[31196]: Failed password for invalid user afar from *EXTERNAL IP* port 60040 ssh21) What is "sshd[port?]"?
2) What is "ssh2"?
Context: This machine has been penetrated recently and used for botneting. I'm trying to be as proactive as possible this time around.
1 Answer
(brute force)
This means that the selection attempt was made from EXTERNAL IP and was not successful.
+ Install Fail2ban DenyHosts.....
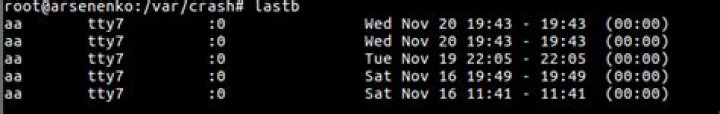
lastb1) What is "sshd[port?]"?
The authlog log file contains the following information:
• date and time: Feb 27 03:02:36;
• server name: bullit;
• remote access server: sshd;
• process pid: 18408;
• username: (phusermv);
• IP address: 77.222.44.2;2- What is "ssh2"?
2 - SSH1 and SSH2 protocols / As already mentioned, sshd can work with the SSH1 and SSH2 protocols. However, the use of unsafe SSH1 is highly discouraged. You can make sshd work only with SSH2: Protocol