DNS servers "ignored" with NetworkManager, systemd-resolved and VPN tunnel
With Ubuntu 20.04, I connect to the internet via WLan using NetworkManager. Then I establish a VPN with OpenConnect.
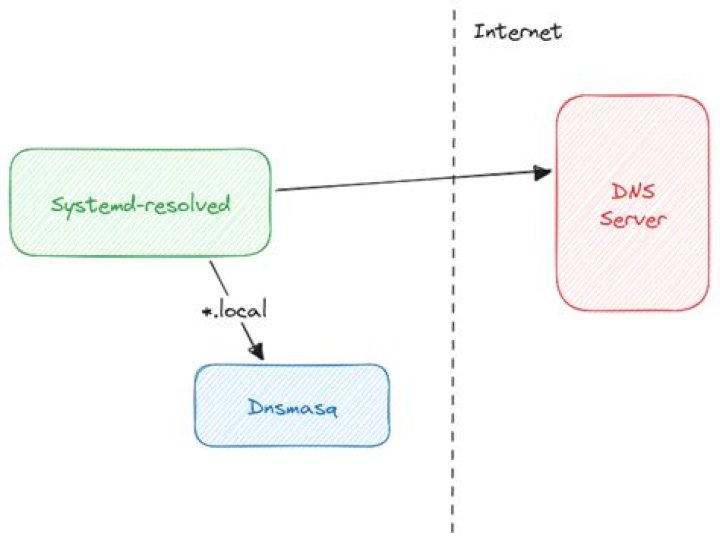
I am using the "stub resolv.conf": /etc/resolv.conf -> /run/systemd/resolve/stub-resolv.conf and I have hosts: files mdns4_minimal [NOTFOUND=return] resolve [!UNAVAIL=return] dns in /etc/nsswitch.conf.
All works fine besides that the DNS 10.233.63.202 of the VPN is not being used:
Link 37 (tun0) Current Scopes: DNS
DefaultRoute setting: yes LLMNR setting: yes
MulticastDNS setting: no DNSOverTLS setting: no DNSSEC setting: no DNSSEC supported: no Current DNS Server: 10.233.63.202 DNS Servers: 10.233.63.202 10.233.63.203Looking at journalctl -u systemd-resolved -f, only the "Current DNS Server" 192.168.3.1 of the WLan link is used:
Link 3 (wlo1) Current Scopes: DNS
DefaultRoute setting: yes LLMNR setting: yes
MulticastDNS setting: no DNSOverTLS setting: no DNSSEC setting: no DNSSEC supported: no Current DNS Server: 192.168.3.1 DNS Servers: 192.168.3.1 10.233.63.202 10.231.76.11 DNS Domain: ~.From what I understand so far is that systemd-resolved may not use a DNS of tun0 because NetworkManager adds the ~. "DNS Domain" to wlo1.
Even if I add it to tun0 with sudo resolvectl domain tun0 ~. and remove it from wlo1 with sudo resolvectl domain wlo1 some.search.tld, no DNS of tun0 is used.
I've even added one of the DNS of tun0 to wlo1 and would expect that it would be used since 192.168.3.1 doesn't have the answer, but it is not the case.
Only when I change the order of the DNS of wlo1 so that i.e. 10.233.63.202 is the "Current DNS Server", hostnames in the VPN are resolved. It appears as if only the "Current DNS Server" of wlo1 is ever consulted.
If the DNS of the VPN link are not used because OpenConnect, NetworkManager and systemd-resolved don't play well together for some reason I can live with that.
But why aren't the other DNS of wlo1 being used? In fact, this worked fine for years up until now.
Also, I am not aware how much I have to be concerned about DNS leakage which probably happens if I add the VPN DNS as "Current DNS Server" of the WLan link?
21 Answer
[Torsten, what's missing in your question is how you would like things to work. So I'll outline some possibilities here and can come back to provide a more complete answer. Something that is odd about your setup is that your VPN DNS providers are listed for your wlo1 interface, though that may not affect anything practical until your current DNS server fails.]
I went through something very similar with network-manager-openconnect on 20.04 LTS and after reading mcatanzaro's blog on VPNs and Split DNS I figured things out enough to make my setup work. Some hints:
- resolved does allow you to change the default DNS Search to a different interface (not sure why yours isn't working yet) but that will indeed leak all lookups to the VPN's DNS server.
- You can test this by using resolvectl directly to set and clear the DNS Domain setting; for instance, below I'm making wlo1 active for DNS searches, and nothing will be queried against tun0:
sudo resolvectl domain tun0 "" sudo resolvectl domain wlo1 "~¨ - If you clear both interfaces' DNS Domain settings — setting both to the empty string — then both interfaces' DNS servers will be queried and if either of them returns an answer that's what you will get. (I'm not sure how it resolves conflicts if they disagree on anything other than NXDOMAIN results.)
- if you don't want to leak your DNS requests, though, then you need to set up DNS Domains to only use the DNS server for a specific subset of domains. You can use
resolvectlas above, or, to change this permanently in your NetworkManager configuration, the confusingly-nameddns-searchconfiguration for that:sudo nmcli con mod vpn0 ipv4.dns-search "~foo.internal,~bar.corp.com" - There's no easy way to do anything more sophisticated then that. You either need to tell resolved to use the VPN's DNS server for a specific set of domains, or leak all DNS queries to it.
Regarding the tilde in the nmcli output, note that the dns-search syntax allows you to specify DNS Domain and DNS Search simultaneously; domains prefixed with tildes don't get added to DNS Search, which I think makes sense or else you may end up accidentally leaking requests that lack FQDNs.