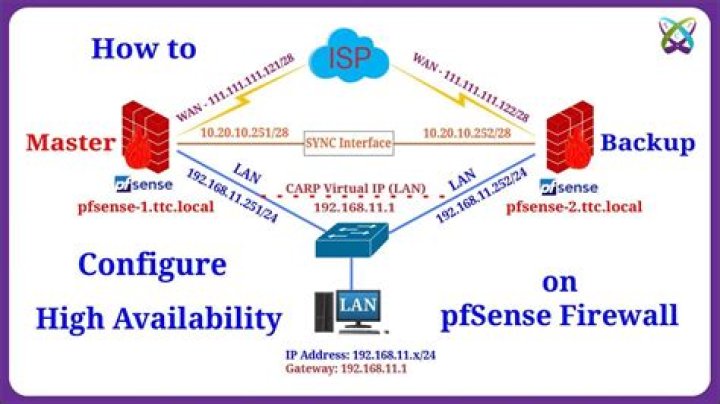
How to configure pfSense as a simple router
I’m working with pfSense 2.5.1 and VMWare Workstation Pro 16.
I’m trying to configure a pfSense vm as a simple router (no firewalling or other stuff) with three NICs:
- em0 = WAN (it is natted)
- em1 = LAN (192.168.10.254 and DCHP enabled on VMNet1 with its DHCP disabled)
- em2 = OPT1 (192.168.20.254 and DCHP enabled on VMNet2 with its DHCP disabled)
Following what I read on Internet, I checked “Disable all packet filtering” and I’ve also disabled Outbound NAT but, I do not know why, the routing does not work: the pfSense machine accesses to Internet without problem (I can ping a remote host via IP or URL from it console) but every machine connected to em1 (VMNet1) or em2 (VMNet2) can’t go on Internet: they get correctly the configuration via DHCP but there is not internet access.
Could you please tell me which are the exact steps for setting a pfSense machine as a simple router without firewall or other stuff enabled?
- MORE -My computer, on which I have Win10 Pro installed with VMWare WS 16, is connected via Ethernet cable to the fiber optic modem. The strange behaviour occurs when there are more that two NICs in pfSense: I mean that if I configure pfSense for using just two network cards (one as WAN and the other as LAN) I have no trouble at all and each device connected to the LAN NIC goes to Internet perfectly just after the installation of pfSense and without any configuration. So, I presume that the upstream gateway is able to handle network connectivity (@user1686). But, if there are more than two NICs , no routing occurs between LAN cards and WAN card (and either the one that worked before installing another NIC , stops working) even if devices get correct config from DHCP and I can ping the WAN IP address from any device connected to one of the LAN cards.
- VIDEO -I just finished to upload a video on Youtube (probably you have to wait to watch it in Full HD):
where you can see exactly what I'm trying to explain: as you'll see, initially pfSense seems to work but after configuring the second LAN card (OPT1) everything stops working.
53 Answers
I assume your WAN is either directly connected to the ISP or the the ISP modem.
In that case the default basic pfSense config (just configuring the interfaces and ip-ranges, nothing else) should be exactly the config you are looking for.
(And that includes outbound NAT. You need that in order for the NAT to the WAN interface to work.)
However, from my own experience with pfSense, once you start playing with the settings and make a mistake it can be very difficult to get back to your original starting point.
I strongly recommend you re-install pfSense from scratch. Define the WAN, LAN and OPT interface with their ip-addreses and ranges during setup and don't touch anything else.
That should bring you to a good starting point. From that point on you can save the pfSense config from the web-interface each time before you make any changes and revert to that save-point if things don't work out as expected.
It's been a while since I setup a pfSense, but going from memory, you just need to do that basic setup.
And maybe add for each internal LAN an "allow any to any" firewall rule to make sure there is no filtering at all and both internal LAN's can talk to each other.
I notice you are doing this in VM's on VMWare workstation.
Make sure that the IP settings that VMWare assigns with its own internal DHCP to the guests are not conflicting with what pfSense wants to use.
In order to use the pfSense the clients must use the pfSense ip-address (in their subnet) as the default gateway and as DNS server. Best to set the clients to manual IP in stead of DHCP. If they are on DHCP they will get their (incorrect) instructions from the VMWare DHCP since you disabled DHCP on the pfSense internal LANs.
In a situation like this is is very easy to mix the intended config on your VM's with the default config supplied by the virtualization product, which can seriously confuse and complicate your troubleshooting process.
If you disable (outbount) NAT you are disabling the function to use one public IP for internet access from several devices in your LAN ("behind" your router). So the current behaviour is actually the correct behaviour.
If you have a single public IP address (usually a dynamic IP) from your ISP which I assume is your scenario, you need to reactivate NAT, in order for the devices "behind" your router to have access to the internet as well.
If you have multiple public IPs (static IPs) you can give the to the devices individually and you need to setup your router accordingly (in this case you can disable NAT).
Note: NAT is only considered a "firewall"-function because, in layman's terms, incoming packets are usually dropped unless you setup a port forward. This can give some network "security" hence the reference to the "firewall". But this is only a by-product of the main reason for using NAT (at least in your scenario) which is to be able to access the internet with multiple devices through one IP address.
Note: You might not get a "real" public IP address from you ISP but a carrier grade NAT address. But this shouldn't cause any issues for any devices in your LAN trying to access the internet (outbound traffic).
Note: You need to setup the router is it knows how to route between networks (specifically between LAN and WAN). It might be easier just to go with a end consumer router where you just have to plug in the WAN and the LAN cable and do very little setup. If you want to stick to your solution I would advice to read up on routers and router setup, a good search term might be setup router routing table. Maybe some basic stuff on routers/layer3 (and layer2) as well. There are tons of resources, depending on your learning preferences e.g. on Youtube
If you are not NATing your outbound traffic from your 192.168.x.x networks to the internet, your ISP will not route this traffic, as this is a non-routable IP range. That's why nothing from these 2 IP address ranges have internet access.