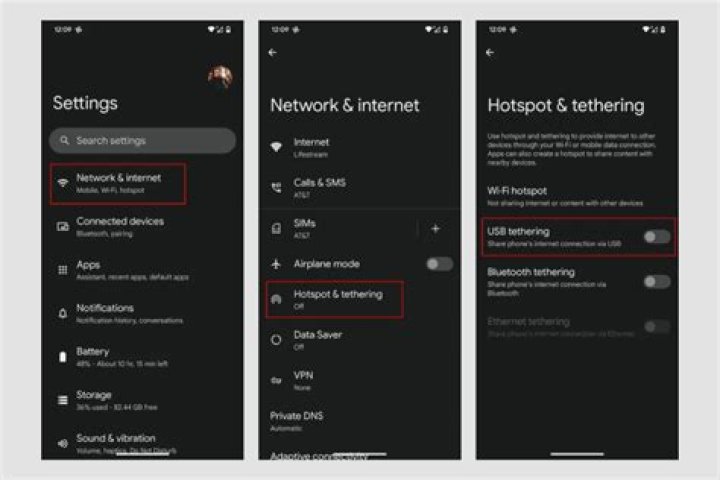
Setting up an open hotspot (via hostapd) that's filtered by mac address while using UFW and custom DNS via dnsmasq
I'm trying to setup what's called a Homepass for my Nintendo 3DS. This basically requires I have the following in play:
- Wireless network with no authentication (open)
- A MAC address cycler (change the wireless cards MAC address after a period of time)
Obviously there are security issues with this - who wants to have an open wireless network. I wanted to mitigate these risks by implementing the following:
- MAC address filtering (Can be spoofed)
- Isolating anything coming in from the wireless network so it cannot access my internal LAN
- Restricting DNS lookups to select addresses (I'm not sure of these just yet, I need to find them out)
- Restrict IP addresses the that can be accessed (Again I'm unsure of these, I need to find them out)
What I currently have setup: - dnsmasq acting as a DNS server and DHCP server for my local network. I'll need to use this for the wireless lan. - UFW as my firewall - A script to cycle the MAC addresses on the wireless card - hostapd running to act as a hotspot
What I'm currently having issues with: - My 3DS is able to connect to the hotspot but it cannot access the internet. To test this out further, I've allowed access to another wireless device on my other PC. It's able to connect, but also not able to access the internet. - My own ignorance. I just don't know how to do some of these things, and due to the nature of my problem my google searches haven't helped all that much.
Existing research: -
What I've done:
Run hostapd via:
sudo hostapd /opt/scripts/nzone/hostapd.confhostapd configuration:
interface=wlan1
driver=nl80211
ssid=NZ@McD1
hw_mode=g
channel=6
auth_algs=1
ignore_broadcast_ssid=0
wpa=0
country_code=CA
macaddr_acl=1
accept_mac_file=/opt/scripts/nzone/allowmacdnsmasq configuration:
# Blocks incomplete requests from leaving the network
domain-needed
# Prevents non-routable private addresses from being forwarded out of the network
bogus-priv
server=/
server=//192.168.0.199
# Upstream DNS servers
server=8.8.8.8 # Google
server=8.8.4.4 # Google
#server=208.67.222.222 # OpenDNS
#server=208.67.222.220 # OpenDNS
# Only queries for private domain are answered by Dnsmasq
#local=/
local=/local/
#domain=home.local
domain=local
interface=eth0
interface=wlan1
listen-address=127.0.0.1
listen-address=192.168.0.199
listen-address=192.168.0.210
# Only listen on the addresses specified with list-address
#bind-interfaces
no-hosts
#no-resolv
addn-hosts=/etc/dnsmasq.hosts #
# Why does the interface command break now? Worked before.
#dhcp-range=interface:eth0;192.168.0.21,192.168.0.100,6h
#dhcp-range=interface:wlan1,192.168.0.240,192.168.0.245,1h
dhcp-range=192.168.0.21,192.168.0.50,6h
# Default gateway
#dhcp-option=3,192.168.0.1
dhcp-option=option:router,192.168.0.1
dhcp-option=option:dns-server,0.0.0.0
#dhcp-option=option:ntp-server,3.ca.pool.ntp.org # This doesn't work.. why?
# Windows/Samba suggestions from default configuration
dhcp-option=option:ip-forward-enable,0
dhcp-option=option:netbios-ns,0.0.0.0
dhcp-option=option:netbios-dd,0.0.0.0
dhcp-option=option:netbios-nodetype,8
#dhcp-option=19,0 # option ip-forwarding off
#dhcp-option=44,0.0.0.0 # set netbios-over-TCP/IP nameserver(s) aka WINS server(s)
#dhcp-option=45,0.0.0.0 # netbios datagram distribution server
#dhcp-option=46,8 # netbios node type
dhcp-leasefile=/var/lib/misc/dnsmasq.leases
bogus-nxdomain=64.94.110.11
dhcp-authoritative
mx-host=home.local,mail.home.local,30
txt-record=home.local,"v=spf1 mx -all"
# For debugging purposes, log each DNS query as it passes through
# dnsmasq.
#log-queries
# Log lots of extra information about DHCP transactions.
#log-dhcp
# Include another lot of configuration options.
conf-dir=/etc/dnsmasq.dMy UFW status:
Status: active
To Action From
-- ------ ----
23/tcp DENY Anywhere
Samba ALLOW 192.168.0.0/24
Anywhere ALLOW 192.168.0.103/udp
Postfix ALLOW Anywhere
OpenSSH LIMIT Anywhere
Calibre ALLOW 192.168.0.0/24
PlexPY ALLOW 192.168.0.0/24
Ubooquity ALLOW 192.168.0.0/24
Syslog ALLOW 192.168.0.0/24
dnsmasq ALLOW Anywhere
Plex ALLOW Anywhere
ZNC ALLOW Anywhere
PlexWebTools ALLOW 192.168.0.0/24
HDHRExtend ALLOW 192.168.0.104
dnsmasq (v6) ALLOW Anywhere (v6)In my /etc/sysctl.conf file I have:
net.ipv4.ip_forward=1I have manually run these commands for iptables:
iptables -t nat -I POSTROUTING -o eth0 -j MASQUERADE
iptables -I FORWARD -i wlan1 -j ACCEPTAnd for completeness, my /etc/network/interfaces:
# The loopback network interface
#auto lo eth0 wlan0 wlan1
auto lo eth0
iface lo inet loopback
# The primary network interface
#iface eth0 inet dhcp
iface eth0 inet static address 192.168.0.199 netmask 255.255.255.0 gateway 192.168.0.1 broadcast 192.168.0.255 network 192.168.0.0 up ethtool -s eth0 wol g dns-domain home.local dns-search home.local dns-nameservers 192.168.0.199
#iface wlan0 inet dhcp
# wpa-ssid SSID
# wpa-psk blargh
# wpa-conf /etc/wpa_supplicant/wpa_supplicant.conf
# pre-up /sbin/wpa_supplicant -B -i wlan0 -c /etc/wpa_supplicant/wpa_supplicant.conf
# post-dwn killall -q wpa_supplicant
#iface wlan1 inet static
# hostapd /etc/hostapd/hostapd.conf
# address 192.168.0.200
# netmask 255.255.255.0
# gateway 192.168.0.1
# broadcast 192.168.0.255
# network 192.168.0.0
# dns-domain home.local
# dns-search home.local
# dns-nameservers 192.168.0.199
# This is an autoconfigured IPv6 interface
iface eth0 inet6 autoI bring my wireless interface up via:
ifconfig wlan1 192.168.0.210 upAnd I change its MAC address via:
ifconfig wlan1 down hw ether $MAC upSome info from the syslog:
Nov 8 16:13:48 ubuntu hostapd: wlan1: STA MACADDRESS IEEE 802.11: authenticated
Nov 8 16:13:48 ubuntu hostapd: wlan1: STA MACADDRESS IEEE 802.11: authenticated
Nov 8 16:13:48 ubuntu hostapd: wlan1: STA MACADDRESS IEEE 802.11: associated (aid 1)
Nov 8 16:13:48 ubuntu hostapd: wlan1: STA MACADDRESS IEEE 802.11: associated (aid 1)
Nov 8 16:14:04 ubuntu hostapd: wlan1: STA MACADDRESS IEEE 802.11: disassociated
Nov 8 16:14:04 ubuntu hostapd: wlan1: STA MACADDRESS IEEE 802.11: disassociated