What is the effect of these changes to /etc/ssl/openssl.cnf
Background: I'm using a tool (sqlpackage) that relies on libssl1.0 (installed per a StackOverflow answer) to connect to a SQL Server instance running in a Docker container. I spent a long time trying to get the connection to work (it was failing with an SSL initialization error) and accidentally stumbled on the following workaround. I'm not sure what the effect is.
I'm running Ubuntu 22.04 and have commented the following line out of /etc/ssl/openssl.cnf:
openssl_conf = openssl_initIt seems to be referring to some other sections (which I've left in but are no longer referred to):
[openssl_init]
providers = provider_sect
...
[provider_sect]
default = default_sect
...
[default_sect]
# activate = 1Based on some other research, I suspect that it's now working because I can make a TLS 1.0 or TLS 1.1 connection (rather than TLS 1.2 only), but I may be way off. I don't really understand how this config file works.
My question: what is the effect of commenting out the line that I've commented out? Could it lead to security vulnerabilities? Is there a way that I can narrow down my changes to reduce the scope to just what I need?
EDIT 1 2022-06-09
Error I see when the openssl_conf... line is included:
*** A connection was successfully established with the server, but then an error occurred during the pre-login handshake. (provider: TCP Provider, error: 35 - An internal exception was caught)
I can provide more detailed diagnostics if that would be useful.
1 Answer
This is an OpenSSL config file that is intended for use with OpenSSL 3.0. All of the provider functionality was added in 3.0 and will not be understood by older versions of OpenSSL. Since you have libssl1.0 (and presumably the matching libcrypto) it doesn't understand these new sections.
A 3.0 provider contains crypto implementations and enables you to plug in different implementations for different purposes (e.g. FIPS validated crypto, or a third party provider such as the "oqs" provider that supplies Quantum safe crypto algorithms). The default config file entries for providers (which you seem to have) actually does very little. It provides the structure so that you can add additional providers if you want and has a section for the "default" provider. But that section has nothing in it (the "activate" line is commented out). That is because if you have no other providers then the default provider will be loaded and activated by default anyway.
So it is safe to comment these lines out. It should have no impact on other packages on your system that use OpenSSL 3.0 and won't impact sqlpackage at all (because it doesn't understand it anyway). It would become problematic later if subsequent updates add real provider config data to that config file. For that reason I would not recommend making the change directly to /etc/ssl/openssl.cnf.
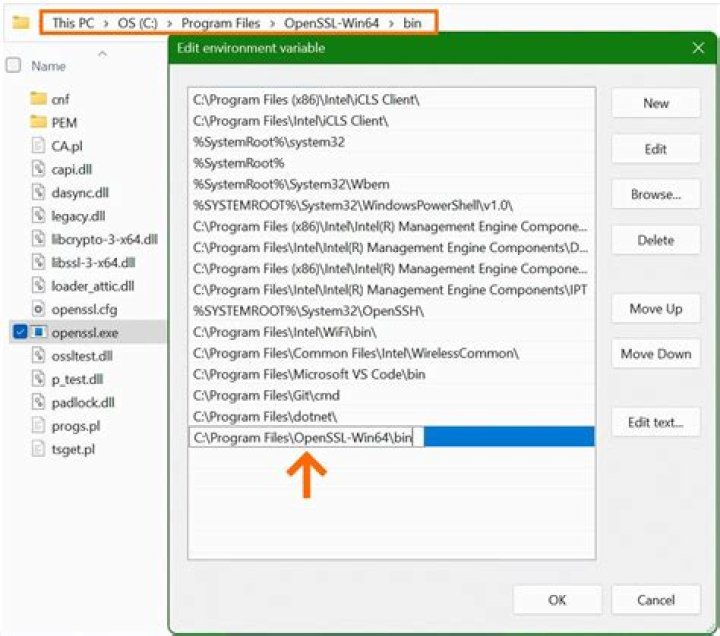
Instead I would take a copy of the default config file and comment out the problematic sections. Start the sqlpackage process with the environment variable OPENSSL_CONF set to point to your custom copy of the config file.
More in general

"Zoraya ter Beek, age 29, just died by assisted suicide in the Netherlands. She was physically healthy, but psychologically depressed. It's an abomination that an entire society would actively facilitate, even encourage, someone ending their own life because they had no hope. Th…"
